Linking Contextual Data Analysis, Data Lineage for Next-gen DLP
What is Contextual Data Analysis in Data Security
Contextual Data Analysis in data security means understanding not only the data itself, but also its surrounding context—who accessed it, from where, when, and how it was used. This deeper visibility supports data lineage, which tracks the entire lifecycle of sensitive information across systems. Traditional DLP struggles with data lineage because it focuses on static rules and content alone. To address modern risks, organizations need updated technologies that combine context with lineage-aware protection.
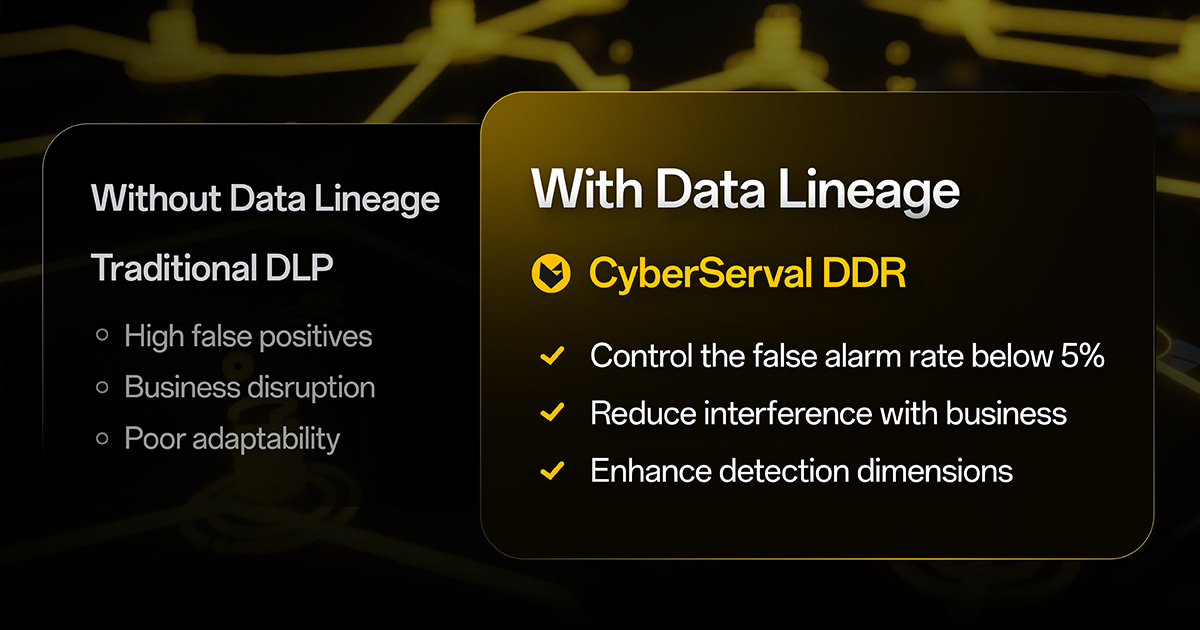
The Challenges for Traditional DLP without Contextual Data Analysis
In today’s digital and cloud-driven environment, data security challenges are more complex than ever. Traditional Data Loss Prevention (DLP) tools, while helpful in the past, are now showing significant limitations.
- High false positives: Keyword or regex matches often misclassify harmless data as sensitive.
- Business disruption: Normal workflows are blocked, leading to employee frustration and conflict with security teams.
- Poor adaptability: With remote work, BYOD, and cloud adoption, content-based DLP can no longer keep up.
The result? Companies spend heavily on DLP but gain little value—worse, they end up alienating their employees.
Overreliance on Content Data
Legacy DLP is built on content inspection methods such as:
- Keyword or regex detection
- File fingerprinting
- Pattern recognition (e.g., credit card formats)
The problems:
- Slight changes in formatting or encoding can bypass detection.
- Ordinary text strings often trigger false positives.
- Newly created sensitive files can be overlooked if not pre-registered.
Lack of Context Awareness
Traditional DLP cannot answer key questions:
- Financial reports → sent to CFO: normal or not?
- Financial reports → sent to a personal Gmail account: risky or not?
Without context, DLP relies on blunt “block everything” policies—disrupting productivity.
Misfit for Modern IT Environments
As businesses embrace hybrid work and cloud services, data boundaries blur:
- Collaboration platforms like Slack, Teams, and Zoom are beyond traditional DLP’s reach.
- BYOD devices and external contractors weaken endpoint coverage.
- Cross-border data transfers require more nuanced compliance controls.
Why does Next-gen Data Loss Prevention Need Data Lineage?
Unlike Content Data, which focuses on what the information contains, Contextual Data, CyberServal data lineage tracks the environment around data use:
- User identity & role: Who is acting? Is it authorized?
- Time & location: When and from where is the data accessed?
- Device & channel: USB, cloud drive, email, printer, etc.
- Action type: Is it sharing, downloading, copying, or external sending?
Solving DLP’s Core Problems
- Reduce false positives: Context validates intent. Example: R&D files sent to an R&D manager (normal) vs. to an unknown email (risky).
- Minimize disruption: Legitimate business activity flows smoothly.
- Spot unknown risks: Even if no rules exist, abnormal context (e.g., midnight file transfer to USB) can trigger alerts.
Real-World Applications
- Financial services: Detect if client data is sent to partners (legitimate) vs. personal accounts (non-compliant).
- Manufacturing: Flag R&D documents copied to USB drives outside work hours.
- E-commerce: Monitor unusual bulk downloads of customer order histories.
How Data Lineage Complements CyberServal Data Security
CyberServal DDR-next gen data security services, integrates and improves various tools, efficiently combining Data Loss Prevention (DLP) with Insider Risk Management (IRM) to achieve integrated endpoint data security management, addressing data leakage issues through "data + behavior" multi-dimension monitoring. In data security detection, it specifically emphasizes the application of contextual data content-CyberServal Data Lineage:
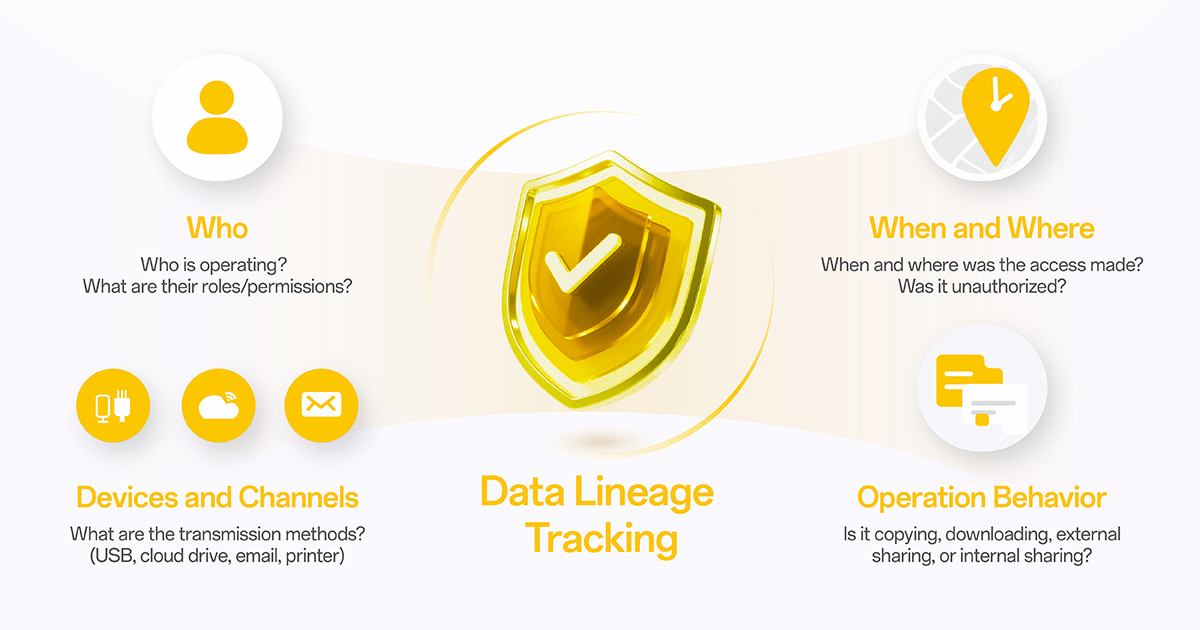
User: Who is operating? What are their roles/permissions?
◦ Device Identity Matching: CyberServal DDR data security can automatically synchronize enterprise employee and device information without employees being aware. DDR data security then automatically establishes the association between employees and their devices without manual intervention. This lays the foundation for refined data security management.
Related Article: Why Traditional DLP Fails in Data Security Management
◦ User Entity Behavior Analytics (UEBA): DDR's UEBA technology can automatically generate user profiles of enterprise employees and departments, thereby accurately locating and identifying high-risk employees. It assesses all risky behaviors by analyzing employees' identities, departments, and statuses.
◦ Integrating HR systems/organizational structures: DDR data security supports synchronizing organizational structures and user information with third-party systems such as AD domains, LDAP, DingTalk, Feishu, and WeCom, enabling automatic binding and management of employees and devices.
◦ Refined policies: It supports integration with local and cloud-based directory services, thus supporting fine-grained policies based on user groups and departments.
Time/Location: When and from where was the access made? Was it unauthorized?
◦ Data Flow Tracking: DDR data securitycan achieve full - link data flow tracking from data download, local processing to external transmission. This means that no matter how data is transmitted, modified, or converted within the internal system, it can be accurately captured and recorded by DDR, and managers can clearly see the complete flow path of the data.
◦ Risk Detection and UEBA: The system can dynamically adjust users' access rights to sensitive files or block abnormal access based on the data leakage risk level, user behavior, and device trust score.
◦ Data Lineage: DDR data security identifies the true importance of data by tracking its source and flow path. It can even infer the importance of data based on its source, processing method, and participants without looking at the data content. For example, it prohibits the external distribution of unpublished financial statements created by the CFO. Even if the content is the same, a higher sensitivity can be assigned based on the source.
Devices and Channels: What are the transmission methods? (USB, cloud drive, email, printer)
◦ Full-channel data stream monitoring: DDR data security comprehensively captures the behavioral data of the operating system (file system, processes, network traffic, clipboard, etc.) through the kernel driver monitoring technology. It can penetrate deep into the application layer transmission interfaces to comprehensively monitor and control various external transmission channels such as USB devices, instant messaging tools (e.g., WeChat, DingTalk), browser uploads, network sharing, email clients, printers, and code repositories (e.g., GitHub, SVN).
◦ Browser Control: DDR data security has multiple technologies for identifying dynamic data transmission in browsers. By combining precise data matching technologies (IDM, OCR, etc.) with multi-dimensional aggregation, it enables the detection, decryption, and content recognition of SSL encrypted traffic, controls file uploads, downloads, and URL access, and effectively intercepts sensitive data within browsers.
◦ Peripheral Management: DDR data security can manage and control the use of external devices such as USB devices, optical drives, Bluetooth, printers, and AirDrop.
◦ Code Repository Control: DDR data security can control the flow of code repositories. For example, it only allows code to be pushed to the company's internal code repository and prevents it from being pushed to employees' personal GitHub repositories.
Operation behavior: Is it copying, downloading, external sharing, or internal sharing?
◦ Kernel driver monitoring: The event collection module of DDR data security captures behavior data through operating system interfaces such as the file system, processes, registry, network traffic, and dynamic libraries. It can capture the operation behaviors of application software and network traffic, thereby achieving data leakage prevention monitoring.
◦ Complete event recording: Cyberhaven DDR data security records every event of each piece of data - every move, copy, edit, and share to fully understand how data flows within the company.
◦ Clipboard Control: DDR data security can monitor and restrict the use of the clipboard and manage the copy - paste operations of sensitive data, supporting the auditing and blocking of clipboard content.
Data breaches can damage your company’s reputation and put you at risk of compliance violations. CyberServal DDR leverages data lineage tracking and AI-powered analytics to monitor sensitive information from creation to usage, detect insider threats early, and keep your data secure across all environments.
➡ Click to download CyberServal Whitepaper and discover the next standard in enterprise data security or you can stay update with our weekly case studies, data security insights about the Sharing Information on Advanced Data Security Services.
Improve Data Security with CyberServal DDR (Next-Gen DLP)
By introducing and applying the above context data, CyberServal DLP system - effectively solves the problems of "excessive blocking" and "false negatives" in traditional DLP.
CyberServal DDR Reduce the false positives
- AI-enhanced detection and deep semantic understanding: DDR adopts an AI content insight engine based on large language models (LLMs) that can perform deep semantic understanding of unstructured data, rather than just surface text matching. Even without explicit keywords, the AI engine can accurately identify sensitive information or specific data patterns, significantly improving the detection accuracy.
- Combined judgment of content and context: DDR combines content analysis and data lineage - that is, where the data comes from, where it passes through, and who processes it - to more accurately identify which data is important and which is not. This approach minimizes false positives caused by common content patterns such as phone numbers and emails.
- User behavior analysis and risk scoring: DDR intelligently learns the user behavior model through UEBA, establishes a behavior baseline, and makes real-time decisions on risky behaviors based on risk algorithms. This enables DDR to control the false alarm rate below 5%.
CyberServal DDR Reduce interference with business
- Distinguish between compliant and suspicious usage: DDR can provide diverse and flexible response strategies based on data of different sensitivity levels and users of different risks, including real-time alerts, blocking, approval, file encryption, and dynamic digital watermarking. For example, most users prefer pop-up reminders and audits, while the usage rate of blocking operations is less than 1%.
- Non-intrusive and low performance impact: The DDR client installation package is small (less than 50MB on the Windows platform) and has low memory usage (less than 100MB), with minimal impact on terminal performance. It can be quickly deployed without affecting system security (no need to disable SIP on macOS), and installation, uninstallation, or upgrade do not require a restart. This ensures that while ensuring data security, interference with business is minimized.
CyberServal DDR Enhance detection dimensions
- Data lineage tracking, even when content is difficult to define: DDR's unique data lineage tracking technology can completely record the lifecycle of each piece of data, making every step from creation to circulation clearly visible. Even if the data is encrypted, compressed, has its format modified, or is transmitted through images, DDR can trace it back to its source and identify important data that traditional tools may miss. This enables DDR to judge risks based on its context (such as data source and user behavior) even when the data content is difficult to pre-define (such as newly developed documents).
- Dynamic adaptation of the AI content insight engine: DDR's AI content insight engine can dynamically adjust its identification strategy based on the text context to ensure accurate content insight in various complex scenarios, including understanding various professional terms and background knowledge.
- User entity behavior analysis: By collecting and analyzing user behavior, DDR can identify internal risks that traditional strategies and AI technologies may miss. It can understand the "big picture" of data flow rather than judging risks based on the outliers of a single action, such as high-risk behaviors like a departing employee downloading a large amount of core data in a short period.
- Data asset discovery: DDR's asset discovery function can automatically discover and sort out unstructured data assets on the terminal, form a data asset map, accurately identify the distribution of sensitive files, and implement data security governance measures for illegal or abnormal storage behaviors.
By combining these technologies and capabilities, CyberServal DDR goes beyond the limitations of traditional DLP and achieves more intelligent, accurate, and business-scenario-oriented data protection.